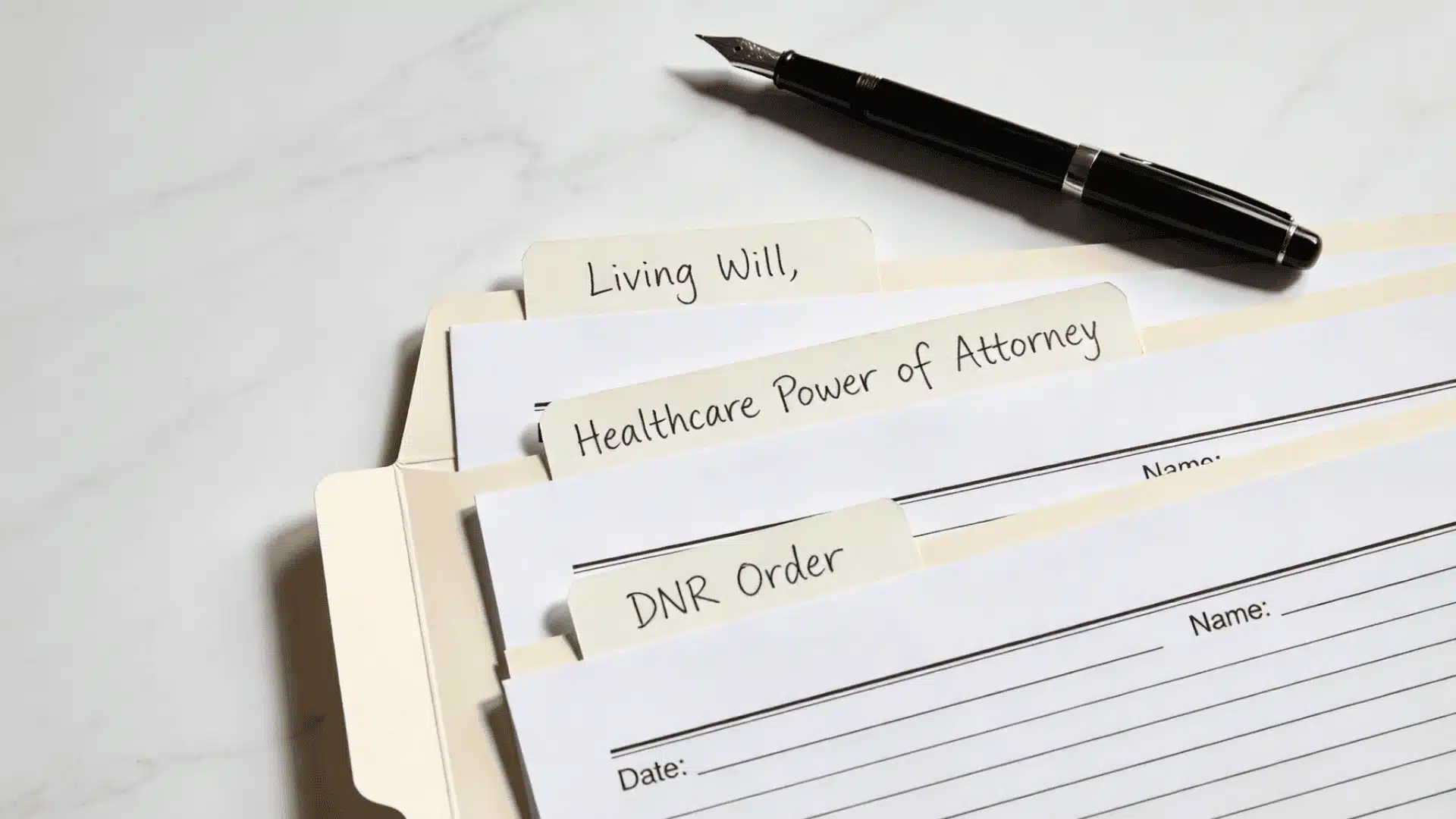
Proprietary information is any business-critical data, process, or knowledge that a company owns, keeps confidential, and derives economic value from, precisely because it is not publicly known.
In today’s data-driven economy, a single spreadsheet, formula, or line of source code can determine whether a company leads the market or falls behind. And when that information walks out the door, the legal consequences follow fast.
Yet many professionals still pause when asked a basic question: what is proprietary information, and why does it carry such legal weight? The answer is not limited to secret recipes or high-tech algorithms.
It extends to internal pricing models, research data, customer lists, and operational methods that are not publicly available.
Misunderstanding this concept can expose a business to compliance failures, contractual disputes, and costly litigation.
Courts do not rely on labels alone. Knowing where the legal boundaries lie is not optional; it is part of responsible governance and risk management in any organization.
What is Proprietary Information & Why Does It Matter?
Proprietary information is business-critical data, processes, or knowledge that a company owns and intentionally keeps confidential because it delivers economic or competitive value.
It includes product formulations and source code, as well as internal strategy and pricing models.
Under 50 U.S.C. § 1708(d)(7), proprietary information covers competitive bid preparations, negotiating strategies, executive communications, internal financial data, strategic business plans, technical designs, manufacturing processes, source code, and other commercially valuable information, provided the owner has taken reasonable measures to keep it confidential and it is not generally known or readily ascertainable by the public.
It matters because it helps businesses stay competitive, safeguard innovations, and maintain customer trust.
When this information is leaked or stolen, companies have lost market dominance, paid multimillion-dollar settlements, and faced federal indictments. This risk applies equally to large corporations, small businesses, and startups.
In my work supporting litigation teams, I have seen this play out more than once: an employee resigns, and within weeks, the former employer is tracking unusual file transfers made in the days before the departure.
What looked like a routine offboarding quickly became a federal trade secret misappropriation claim.
When an engineer walks out the door with source code or manufacturing formulas, that is not just an internal policy breach; it may constitute a federal offense under 18 U.S.C. § 1832of the Economic Espionage Act.
The most common trigger for proprietary information disputes is a departing employee.
Former employees who take confidential data to a competitor, whether through email forwarding, USB downloads, or cloud syncing, account for the majority of trade secret misappropriation cases filed each year.
What Constitutes Proprietary Information?
![]()
Proprietary information includes nonpublic data or knowledge that a business owns and uses to preserve competitive advantage.
It is defined not just by what it contains, but by how it is owned, valued, controlled, and protected. Certain elements determine whether the information qualifies as proprietary in legal settings.
For information to qualify for legal protection, two conditions must be met, drawn directly from the DTSA and the Uniform Trade Secrets Act adopted by 49 states:
- The information must derive independent economic value from not being generally known or readily ascertainable through proper means.
- The owner must take reasonable measures to maintain secrecy, including access controls, confidentiality agreements, and internal compliance policies.
Publicly available information, general industry knowledge, independently developed data, or material disclosed without protective safeguards typically falls outside statutory protection.
Critically, if a company fails to take those reasonable protective steps, it may forfeit statutory protection entirely, and courts will not shield information that the owner treated carelessly.
One thing worth emphasizing: a label alone does not create legal protection. Stamping “proprietary” on a document means nothing if access is unrestricted and no confidentiality agreement is in place.
Common Types of Proprietary Information
Proprietary information appears in many forms across different industries. In everyday business operations, companies rely on several types of protected information to maintain stability.
1. Trade Secrets
Trade secrets include formulas, source code, algorithms, recipes, and manufacturing processes that give a company its competitive edge.
Their value lies entirely in remaining confidential, and unlike patents, they require no public disclosure, only secrecy and reasonable security measures.
A well-known real-life example is Coca-Cola’s original beverage formula, which has been kept secret for over a century.
Companies protect trade secrets through NDAs and strict internal controls. Once disclosed, the advantage is lost, and legal remedies may be the only recourse.
Trade secrets are a legally defined subset of proprietary information, not the same thing. While all trade secrets are proprietary information, not all proprietary information rises to the level of a statutorily protected trade secret.
The distinction matters when determining whether federal or state law applies and what remedies are available.
2. Business and Financial Information
This includes financial statements, profit margins, pricing strategies, sales forecasts, budgets, and investment plans.
Competitors could use this information to undercut pricing or predict market moves. Because of this risk, companies limit access to executives and authorized employees only.
A notable real-life example is Amazon’s internal pricing algorithms, which dynamically adjust millions of product prices and are closely guarded from competitors.
Protecting financial information supports long-term strategic stability and prevents rivals from gaining an unfair advantage in the marketplace.
3. Customer and Client Data
Customer lists, purchasing history, contact details, and client contracts are valuable proprietary assets.
This type of information helps businesses build strong relationships and tailor services to specific needs. If competitors gain access to this data, they could target those customers directly.
When LinkedIn sued hiQ Labs for scraping its user data, arguing that it constituted proprietary information was one of its examples.
Failing to protect customer data not only risks competitive harm but also exposes businesses to serious legal and reputational consequences.
4. Research and Product Development Information
Research findings, prototypes, product designs, and development plans also qualify as proprietary information.
These materials often represent years of investment, testing, and innovation.
A real-life example is Apple’s extreme secrecy around unreleased iPhone models, and even internal teams operate on a need-to-know basis.
Protecting R&D information preserves the financial return on innovation and maintains a company’s first-mover advantage in competitive markets.
5. Sales & Go-to-Market Strategies
Marketing plans, campaign strategies, sales playbooks, target audience research, and product launch timelines are all forms of proprietary information.
These materials reveal how a company acquires customers and positions itself in the market.
If exposed before execution, competitors can counter the strategy or launch first.
A real-life example is Pepsi’s internal marketing campaigns, which are developed under strict confidentiality before launch to prevent Coca-Cola from gaining advance insight.
6. Operational Processes and Internal Systems
Operational procedures, workflow systems, proprietary software tools, and training materials define how a company functions with efficiency and consistency.
Though they may appear routine, they often reflect years of refinement that reduce costs or boost productivity.
A real-life example is McDonald’s standardized operational manuals, which detail every aspect of food preparation and service delivery and are tightly controlled.
Businesses protect this knowledge through restricted platforms and internal documentation policies to prevent sensitive methods from becoming publicly accessible.
How Proprietary Information is Protected?
Proprietary information is protected through layered legal and technical safeguards.
At the contractual level, companies use non-disclosure agreements, confidentiality clauses, and restrictive covenants to impose binding obligations on employees, vendors, and partners.
These agreements define scope, duration, and permitted use. Statutory protection is equally critical.
The Defend Trade Secrets Act of 2016 (DTSA) was a landmark shift; it was the first federal law that gave trade secret owners the ability to file suit in federal court, pursue civil seizure of misappropriated materials, and seek injunctive relief anywhere in the United States.
State-level protection flows from the Uniform Trade Secrets Act, adopted in 49 states. New York remains the only state that relies on common law rather than a codified statute, which means litigation there requires navigating case precedent rather than a single written law.
Protection does not rely on contracts alone. Organizations implement access control lists, role-based permissions, encryption protocols, data loss prevention systems, and audit logs.
Courts assess whether reasonable measures were taken to maintain secrecy before granting relief. Documented compliance practices, therefore, carry significant legal weight.
Criminal penalties under the Economic Espionage Act are significant. Individuals who steal trade secrets for commercial gain face fines of up to $500,000 and up to 10 years’ imprisonment. Corporate fines can reach $5 million.
When the theft benefits a foreign government or agent, those penalties increase, corporate fines can double, and prison terms can extend to 15 years. All property used in the theft and proceeds derived from it can be seized by the government.
What is the Difference Between Proprietary Information and a Trade Secret?
These three terms represent different levels within the same concept. Proprietary information is the broadest, covering all business-owned information that provides value.
Confidential information is a subset that is restricted and shared under obligations of secrecy.
Trade secrets are the most narrowly defined, protected under federal law only if they have independent economic value from secrecy and are actively safeguarded. If those protections lapse, trade secret status is lost.
Proprietary vs Confidential Information
Both are related but not identical, while proprietary information is often confidential, not all confidential information is proprietary. The distinction matters in legal and contractual settings.
| Basis | Proprietary Information | Confidential Information |
|---|---|---|
| Meaning | Information owned by a company that provides economic or competitive value. | Information that is required to be kept private under a duty of confidentiality. |
| Ownership | Must be owned or controlled by the business. | May belong to any party; focus is on privacy obligation. |
| Scope | Includes trade secrets, internal processes, technical data, and strategic plans. | Includes personal data, business communications, and sensitive shared information. |
| Legal Basis | Protected under trade secret laws and contractual agreements. | Protected mainly through contracts, privacy laws, and confidentiality clauses. |
| Independent Economic Value requires | a core qualifying element. | protection arises from the duty of confidentiality, not from economic value. |
What Happens If Proprietary Information is Stolen?
If proprietary information that qualifies as a trade secret is misappropriated, the owner can pursue both civil and criminal remedies.
Civilly, under the DTSA, a company can seek injunctive relief to stop the misuse immediately, recover compensatory damages for actual losses, and, in cases of willful and malicious theft, pursue exemplary damages up to twice the compensatory amount.
Understanding the full scope of the litigation process helps business owners recognize what to expect once a trade secret claim is filed.
Criminal prosecution under the Economic Espionage Act can result in substantial fines and federal imprisonment.
The Department of Justice handles criminal trade secret cases, and convictions carry significant consequences for individuals and organizations alike.
Common Misconceptions About Proprietary Information
Proprietary information is frequently misunderstood in legal and business contexts. Many assume all company data qualifies automatically or that labeling alone ensures protection.
- All internal company information is proprietary: Only information with economic value and controlled secrecy qualifies legally.
- Proprietary information is identical to trade secrets: Trade secrets are a legally defined subset under federal statute.
- Registration is required for legal protection: No formal registration required; protection depends on maintained confidentiality measures.
- Confidential labels automatically ensure legal protection: Labels alone are insufficient without documented security controls and compliance practices.
- Public disclosure does not affect protection rights: Unauthorized public disclosure may terminate trade secret statutory protection.
- Non-compete agreements are not a substitute for trade secret protection. California, for example, does not enforce non-competes. Companies operating there must rely entirely on proving misappropriation of specific protected information, making internal controls and NDAs even more critical.
Conclusion
Understanding what is proprietary information is essential for anyone involved in business, innovation, or information management.
Proprietary information derives independent economic value from remaining confidential. Federal laws have established the framework for enforcement, remedies, and liability.
Courts evaluate secrecy efforts before granting statutory protection.
When properly safeguarded, proprietary information strengthens competitive positioning and supports long-term operational stability.
When mishandled, it can result in litigation, financial damages, and reputational harm.
When operating a startup or managing a large enterprise, recognizing what qualifies and implementing protective controls is a legal and strategic responsibility.
Have you encountered issues involving proprietary information, compliance challenges, or internal safeguards? Share your experience in the comments below.